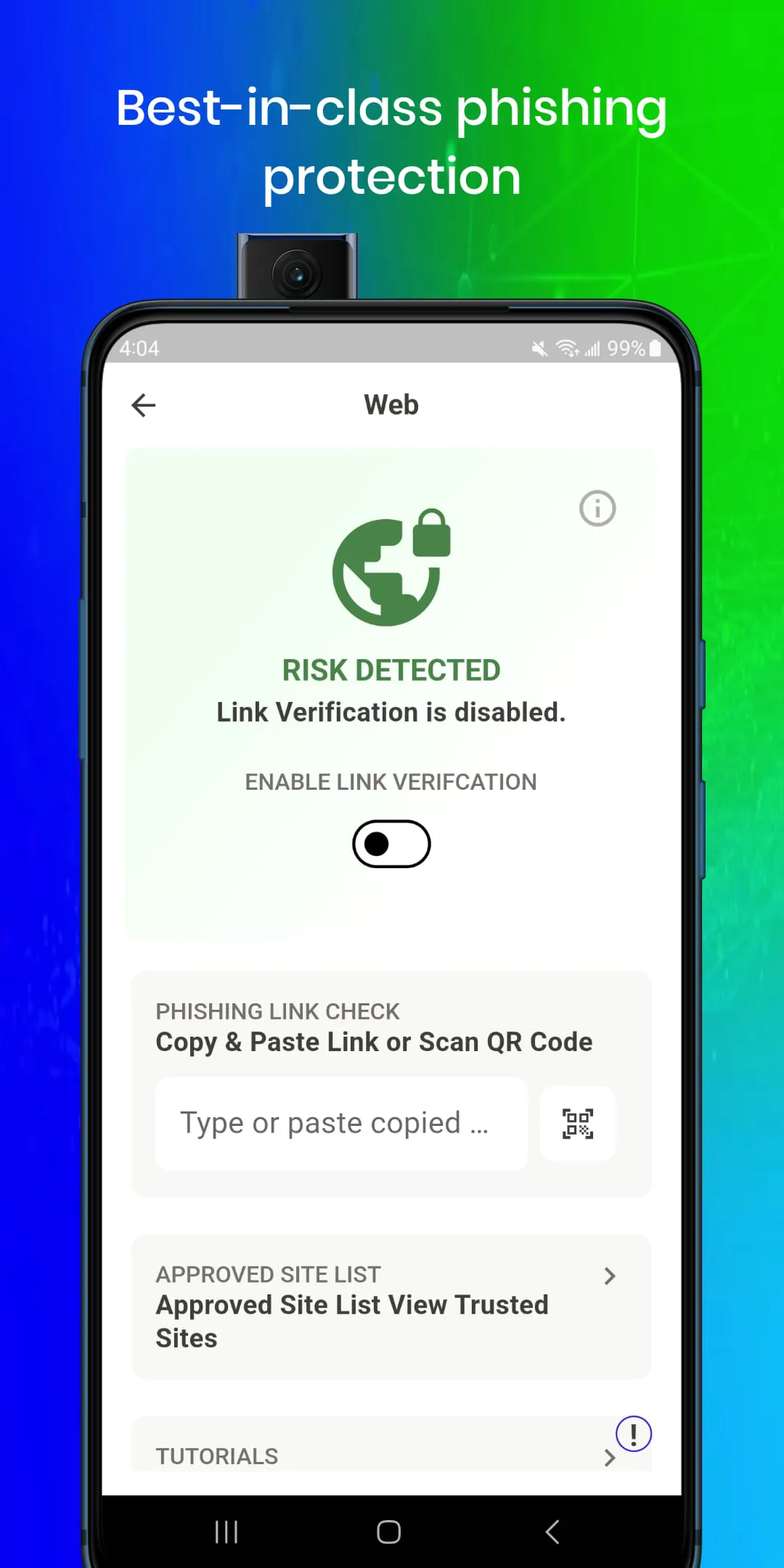
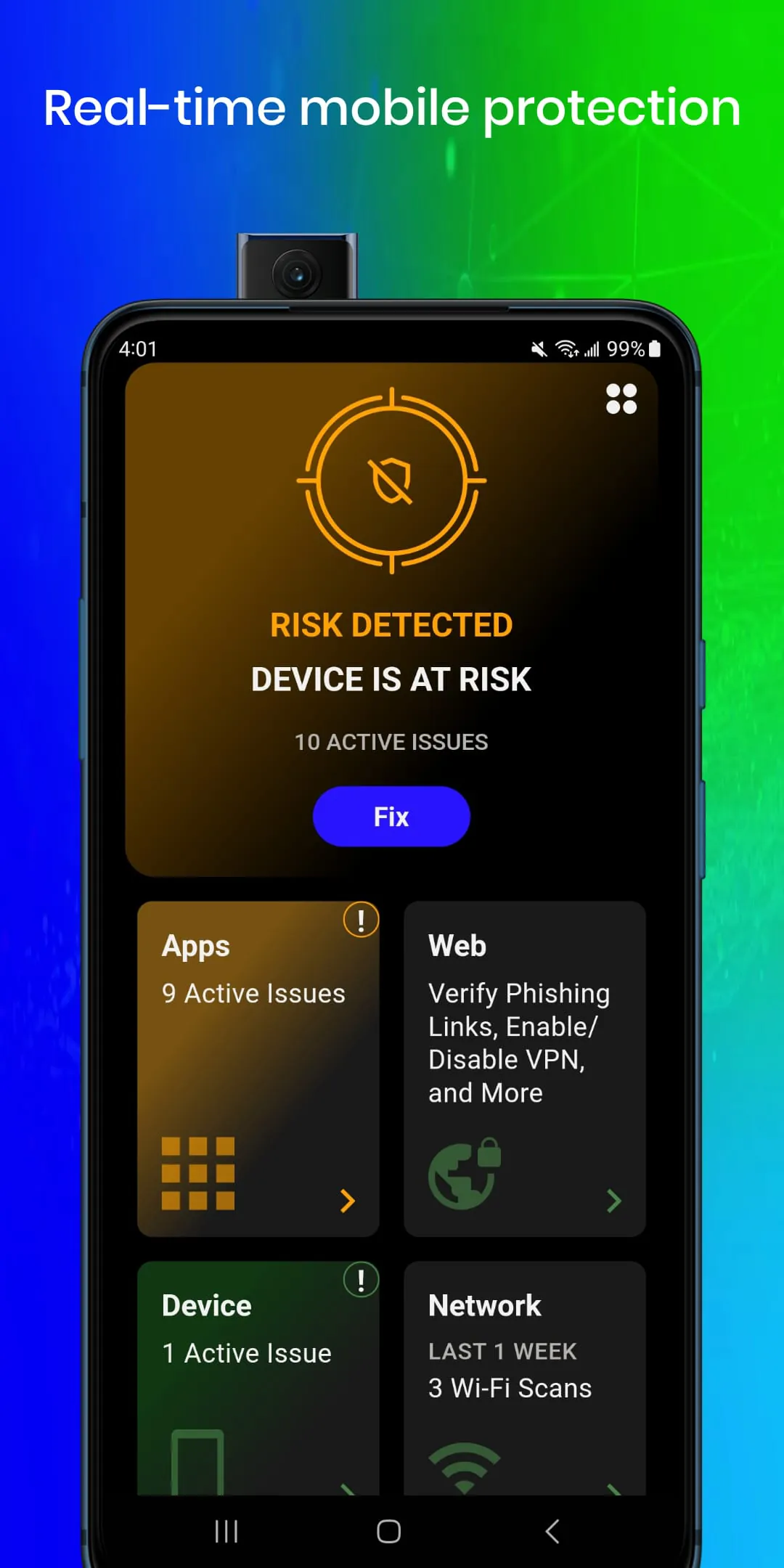
Trellix Mobile Security is a robust, privacy-centric application designed to provide comprehensive mobile security solutions to enterprises. This sophisticated application focuses on safeguarding employee devices and sensitive information from a wide array of threats, including device-level attacks, network intrusions, malicious applications, and phishing attempts. Central to Trellix Mobile Security’s effectiveness is its commitment to maintaining a high level of user privacy while simultaneously delivering top-tier security. The application is engineered to support both Bring Your Own Device (BYOD) and corporate-owned device environments, ensuring that organizations can implement comprehensive security measures without infringing on employees' personal data or privacy rights. This balance between security and privacy is achieved through a carefully designed architecture that prioritizes the collection of threat-related information while strictly limiting access to personal data. Trellix Mobile Security employs a Dynamic Detection Engine, which is continuously enhanced through machine learning algorithms and ongoing security research. This engine enables the application to adapt to the evolving threat landscape and effectively protect devices against even the most sophisticated and advanced attacks. The application’s scalability is a key advantage, allowing it to meet the dynamic security needs of the modern workforce, regardless of the size or complexity of the organization. By focusing on proactive threat detection and prevention, Trellix Mobile Security minimizes the risk of data breaches and other security incidents that can compromise sensitive corporate and personal information. Furthermore, the application is designed to be user-friendly and unobtrusive, ensuring that employees can use their mobile devices without experiencing significant performance slowdowns or disruptions to their daily workflows. The installation and configuration process is straightforward, and the application operates seamlessly in the background, providing continuous protection without requiring constant user intervention. Trellix Mobile Security's architecture is also designed to integrate with existing enterprise security infrastructure, allowing organizations to leverage their existing security investments and create a unified security posture. This integration capability simplifies security management and improves overall visibility into the mobile threat landscape. The application provides detailed reporting and analytics, giving security teams the insights they need to quickly identify and respond to potential threats. Overall, Trellix Mobile Security offers a comprehensive and privacy-conscious approach to mobile security, empowering enterprises to protect their employees and data in an increasingly mobile-centric world. It acts as a shield, defending against a multitude of digital dangers, ensuring business continuity and preserving user trust. The core principle is ensuring security measures do not compromise individual rights, offering a harmonious blend of protection and respect for personal space. This commitment establishes Trellix Mobile Security as a dependable and reliable solution in the ever-evolving sphere of mobile security.
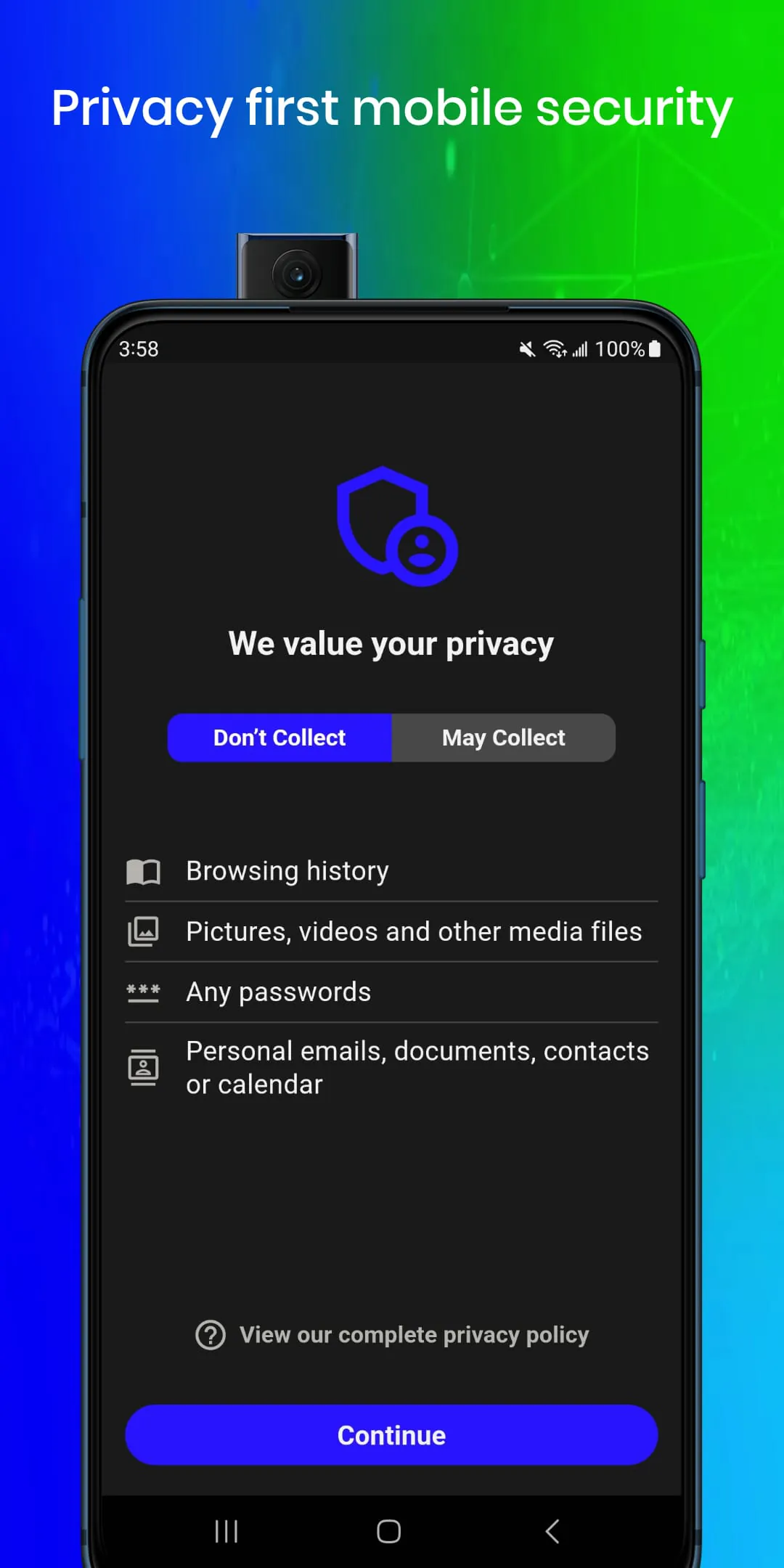
One of the key differentiators of Trellix Mobile Security is its unwavering commitment to user privacy. The application is designed to operate with minimal access to personal data, ensuring that employees' privacy is respected at all times. Specifically, Trellix Mobile Security is engineered so that the user’s organization cannot access the content of texts, emails, or other communications. This means that the application does not monitor or record the content of personal conversations or any sensitive data exchanged through messaging platforms. In addition, the user’s organization cannot view the browsing history of employees using Trellix Mobile Security. This ensures that employees' online activities and personal browsing habits remain private and confidential. The application also prevents the organization from listening to calls or accessing information about who employees are communicating with. This protects the privacy of phone calls and prevents the organization from tracking an individual's communication patterns. Trellix Mobile Security also incorporates strict measures to prevent unauthorized access to the device's microphone and camera. The application ensures that the organization cannot listen to employees through the phone's microphone or monitor them via the camera without their explicit knowledge and consent. Furthermore, Trellix Mobile Security protects the user's files and documents, preventing the organization from reading or accessing personal files stored on the device. The application also ensures that the organization cannot capture the screen or view the contacts stored on the device. These privacy protections demonstrate Trellix's commitment to providing a secure mobile environment without compromising user privacy. It strikes a balance between security needs and individual rights, fostering trust and confidence among employees. The focus on privacy is not merely a feature but a core design principle, reflecting a broader understanding of the ethical implications of mobile security. This approach distinguishes Trellix Mobile Security from other solutions that may prioritize security at the expense of privacy. By implementing these robust privacy controls, Trellix empowers organizations to provide a secure mobile environment while upholding the highest standards of user privacy. The result is a solution that not only protects against mobile threats but also strengthens employee trust and fosters a positive security culture. The commitment to privacy underscores the application's user-centric design, ensuring that the mobile security solution is both effective and respectful of individual rights.
While Trellix Mobile Security prioritizes user privacy, it also collects threat information and system actions to enable the security team to detect malicious activities or attacks that may compromise personal and corporate information. This data collection is conducted in a responsible and transparent manner, with a clear focus on identifying and mitigating potential security threats. The information collected is used to analyze system behavior, detect anomalies, and identify potential indicators of compromise. By monitoring system actions and collecting threat intelligence, the security team can proactively identify and respond to security incidents before they cause significant damage. Trellix Mobile Security ensures that any information collected on the device is never shared or sold to third parties. This commitment to data protection is a key differentiator and demonstrates Trellix's commitment to maintaining the trust of its users. The application is designed to comply with all relevant data privacy regulations, ensuring that personal information is handled in a secure and responsible manner. The data collection process is transparent, and users are informed about the types of information that are being collected and how it is being used. This transparency helps to build trust and ensures that users are aware of the security measures that are in place to protect their data. Trellix Mobile Security also provides organizations with the tools they need to manage and control the data collection process. Organizations can configure the application to collect only the information that is necessary to meet their security needs, minimizing the impact on user privacy. The application's architecture is designed to ensure that data is stored securely and that access is restricted to authorized personnel. This helps to prevent unauthorized access to sensitive information and ensures that data is protected from loss or theft. Overall, Trellix Mobile Security offers a balanced approach to mobile security, combining robust threat detection capabilities with a strong commitment to user privacy. This approach enables organizations to protect their employees and data without compromising individual rights or eroding trust. The careful balance between security and privacy is a key factor in the application's success and makes it a valuable tool for organizations that are looking to secure their mobile workforce.








 4.20
4.20 Download
Download